continuous
investigation
The agentic SOC designed for AI-speed. Mate creates your unique security context graph, enabling Mate's agents to build detections and run triage, investigations, and response, as one, continuous cycle, improving with every alert, tailored for your context.
Get a demo











traditional SOC architecture has collapsed



data is pouring

The SIEM approach has failed. Costs are shooting through the roof. Organizations are migrating to data lakes. Data is distributed across lakes, point solutions, and proprietary systems.

detections turn into security holes

Manual detection engineering cannot keep up with changing context. Rules decay when context changes, creating more noise than value.


investigations break at machine scale

Detection noise, alert volumes, struggling MSSPs and internal skill gaps prevent SOCs from covering all alerts, while investigations cannot keep up with machine-speed attacks.

but traditional solutions are missing one thing:
a context structure

Traditional AI agents try building context in real-time during an incident. This is just like asking an analyst to relearn a new environment on every investigation.


AI SOC built on
your context
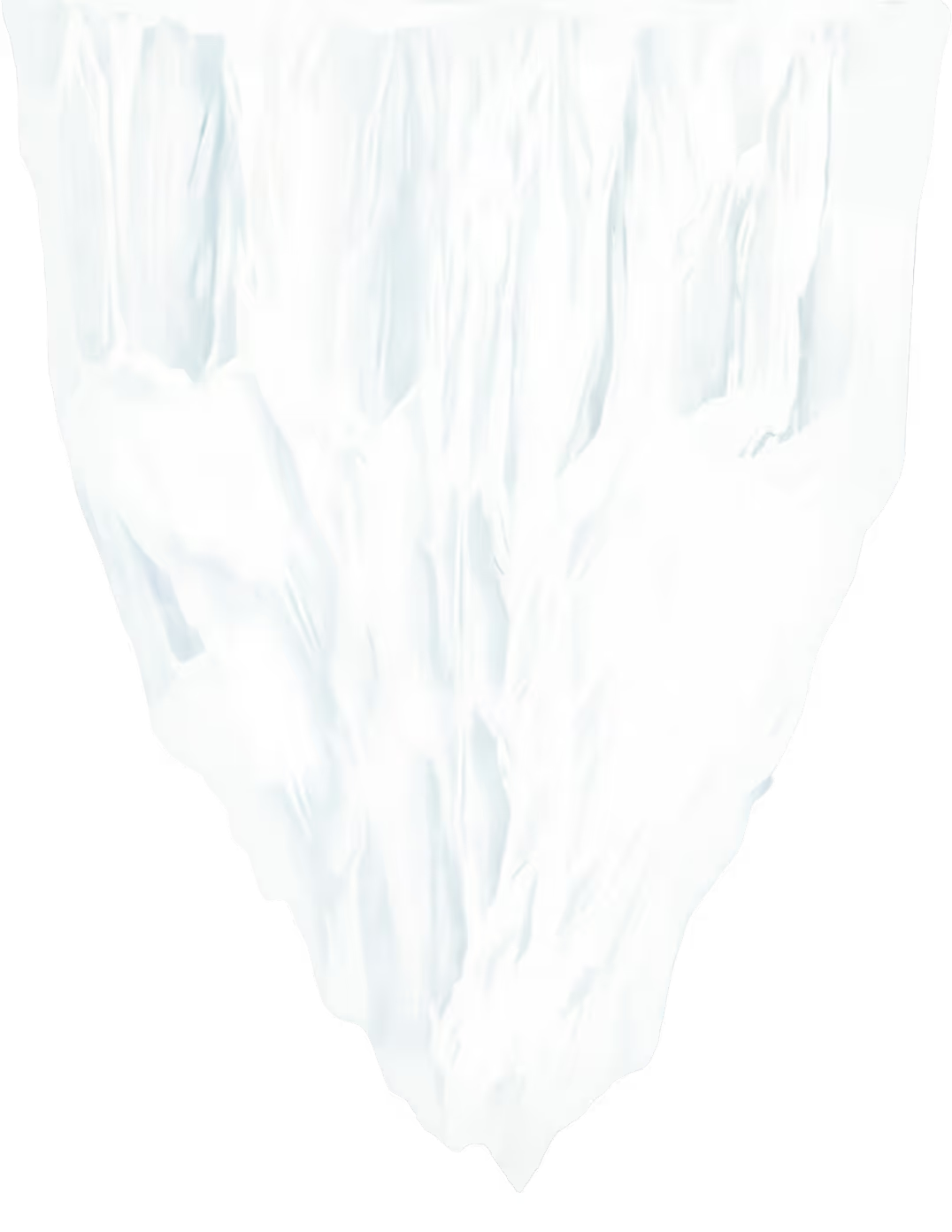

the security context graph
When Mate integrates, it builds a context graph within 24 hours. This is your unique, organizational "brain". Agents use the graph as their knowledge source for investigating, responding, and building detections.
Now, agents can finally operate at elite level, in every investigation.



Data structured for humans, across tables, logs and documents.


The process of transforming data into context: memories that connect the dots, a canonical set of answers for every investigation question.
A living and breathing reflection of your collective institutional memory.
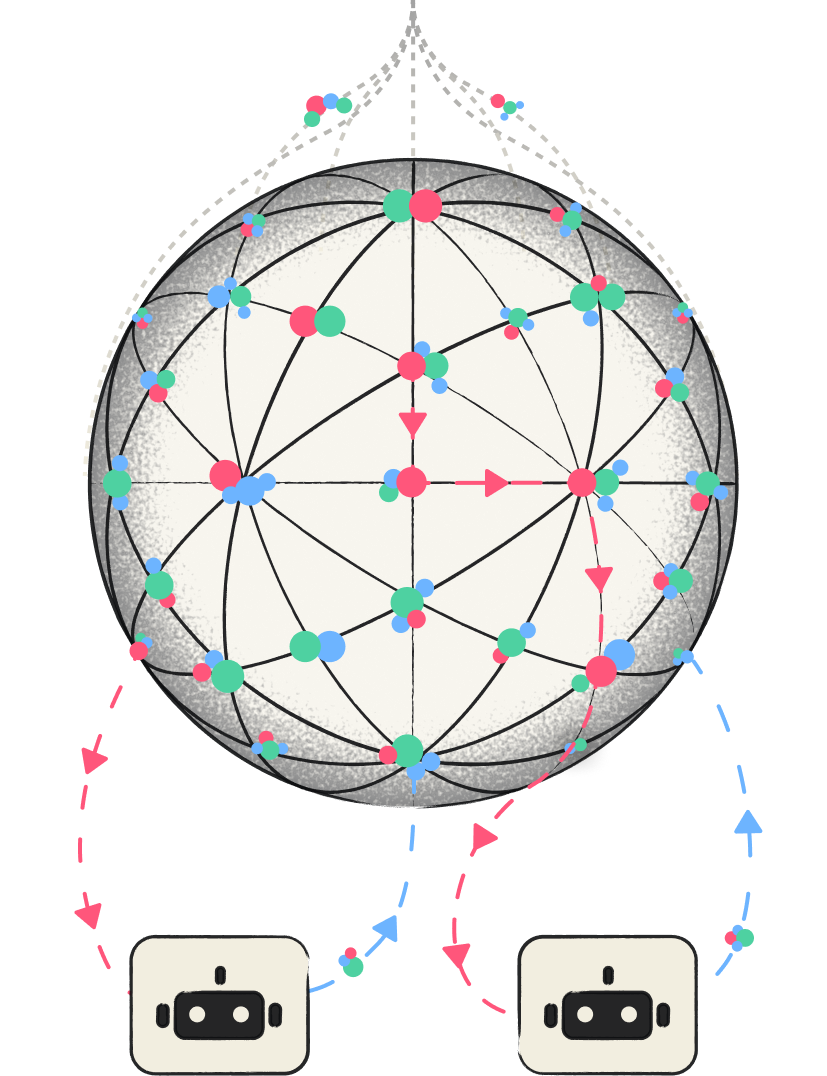
Agents fetch memories to run precise and fast investigations. Their input is fed back into the Graph, continuously evolving the institutional memory.
The New,
Context-Powered SOC
tailored
Detections and investigations built for your SOPs, your architecture, your crown jewels, your threat model. Not generic, rigid data.
smarter
Retains the collective knowledge of your most experienced analysts, gets smarter with every investigation, without restarting each time.
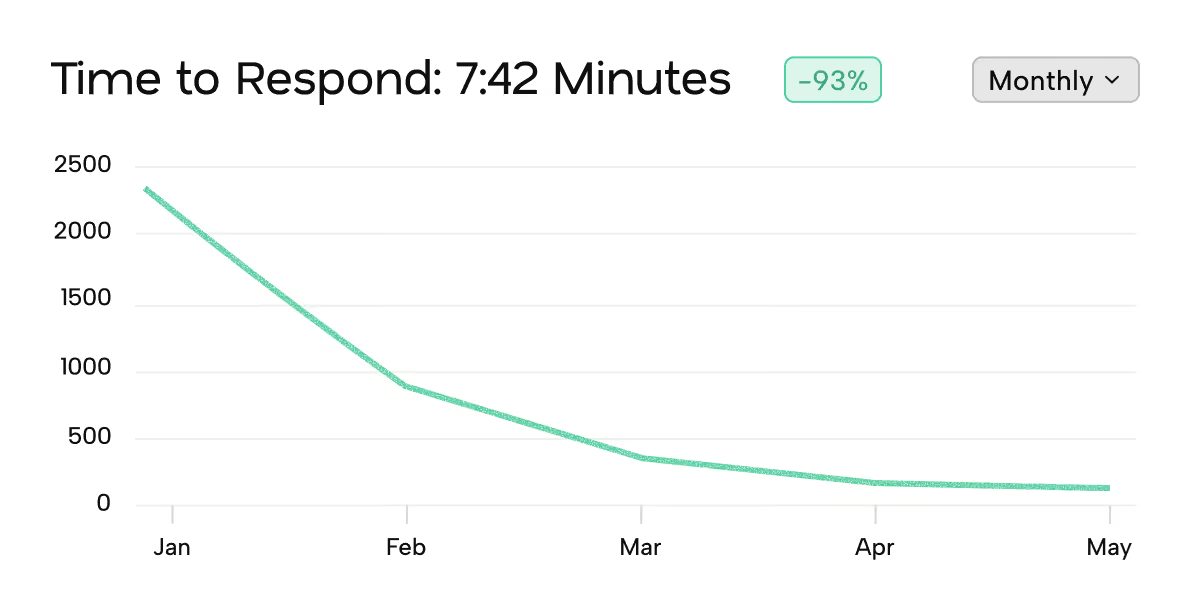
faster
Operates at machine scale: onboards in 24 hours, investigates in minutes, and covers 100% of the alert queue.
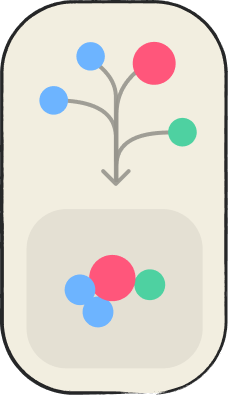
continuous detection / continuous response

CD/CR is a closed-loop framework where AI investigations continuously compress into detections, and detections continuously feed the next investigation. The result: detections and investigations that are rooted in your reality, always-updated as context changes.
Mate in action
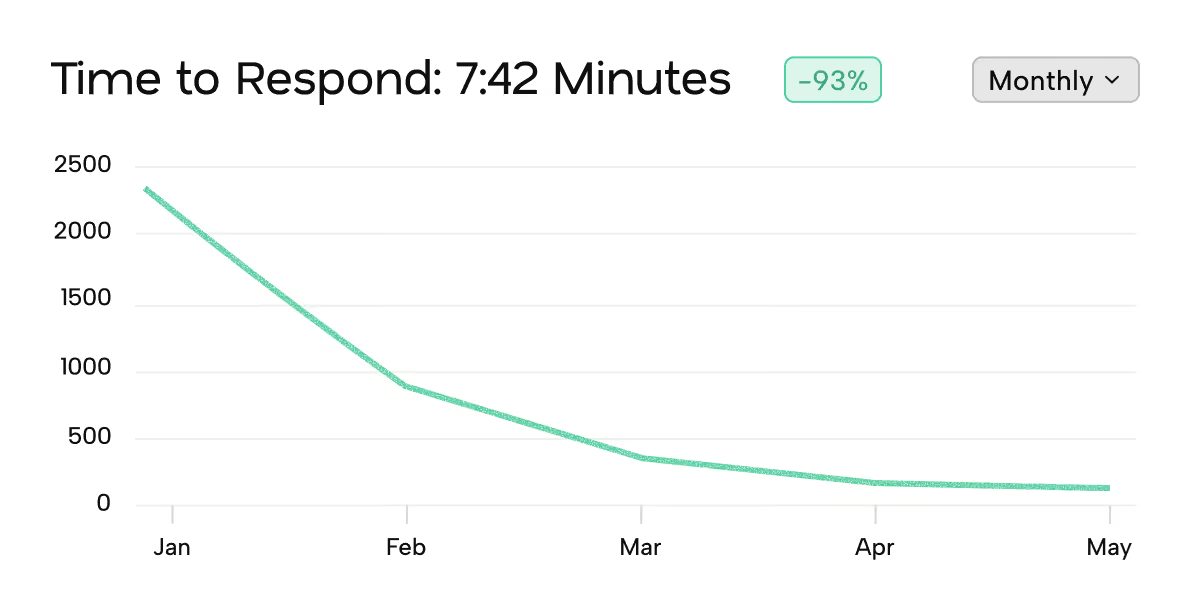
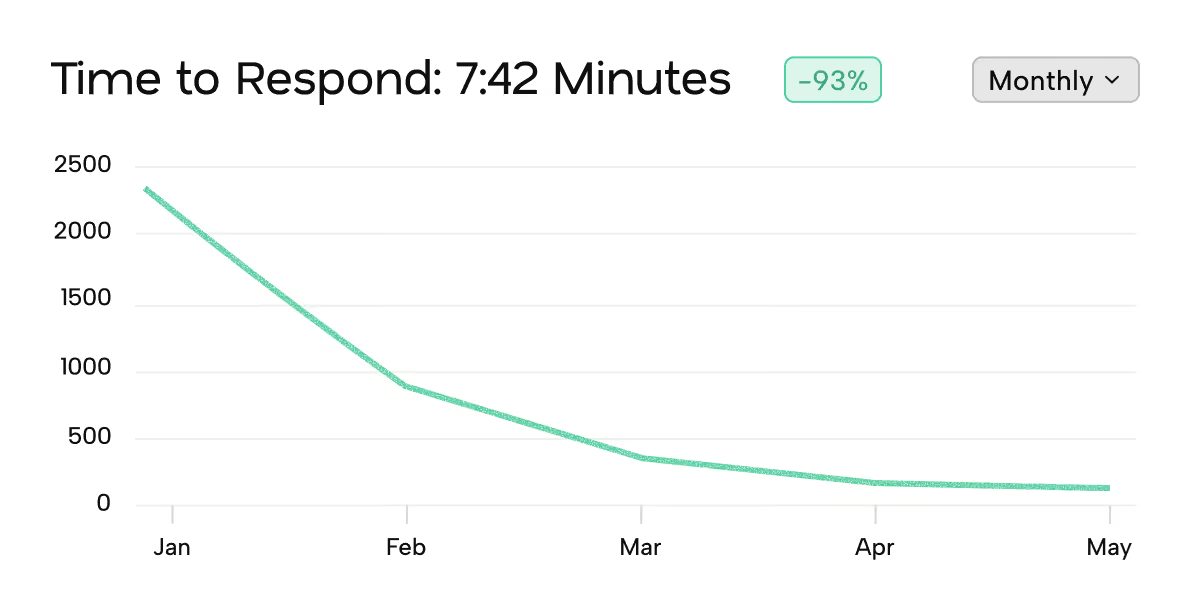
reveal operational and board-level insights
Uncover hidden insights, zoom in on operational bottlenecks and prove ROI to your management and board.
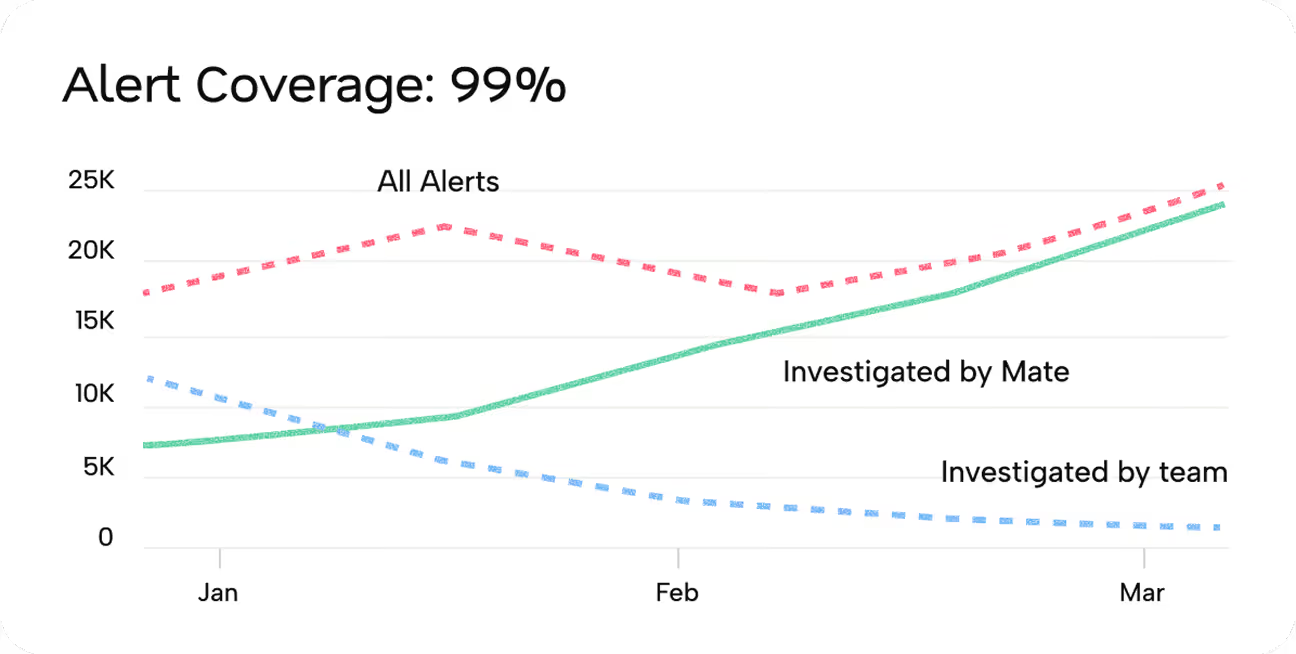

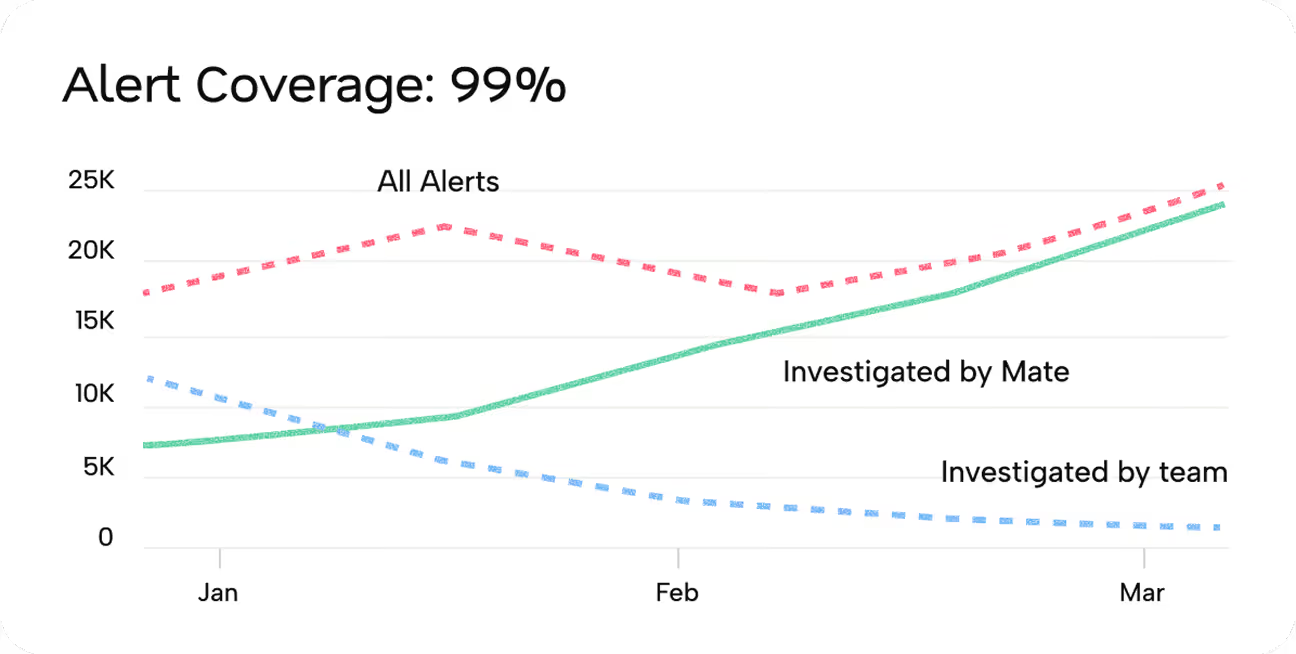

no alerts left behind
Investigate 100% of your alerts. Yes - even the informational ones!
eliminate redundant noise
Mate closes the false positives, while you focus on your threats
respond before it’s too late
Outpace attackers with context-led investigations

the consensus of masters
“Mate is one of the few AI SOC platforms with a differentiated underlying architecture: their knowledge-graph is the actual foundation of the product, building a Security Context Graph from one simple integration.”