
- Supply chain attack leveraged compromised Axios package: A malicious npm package acted as a dropper, deploying a Python RAT, establishing persistence, and self-deleting while targeting CI/CD environments with access to sensitive code and secrets.
- Immediate, automated triage enabled rapid prioritization: Mate’s agents pre-investigated the alert, reconstructed the attack chain, and elevated it to P0 without manual enrichment or tool-switching by analysts.
- Full execution chain visibility confirmed attacker actions: The system traced all stages from package installation to RAT deployment and self-deletion, providing a complete and attributed view of the attack sequence.
- Secrets exposure and blast radius were assessed instantly: Mate analyzed connected cloud resources and CI/CD dependencies to identify potential credential exposure, enabling precise and prioritized remediation actions.
Overview
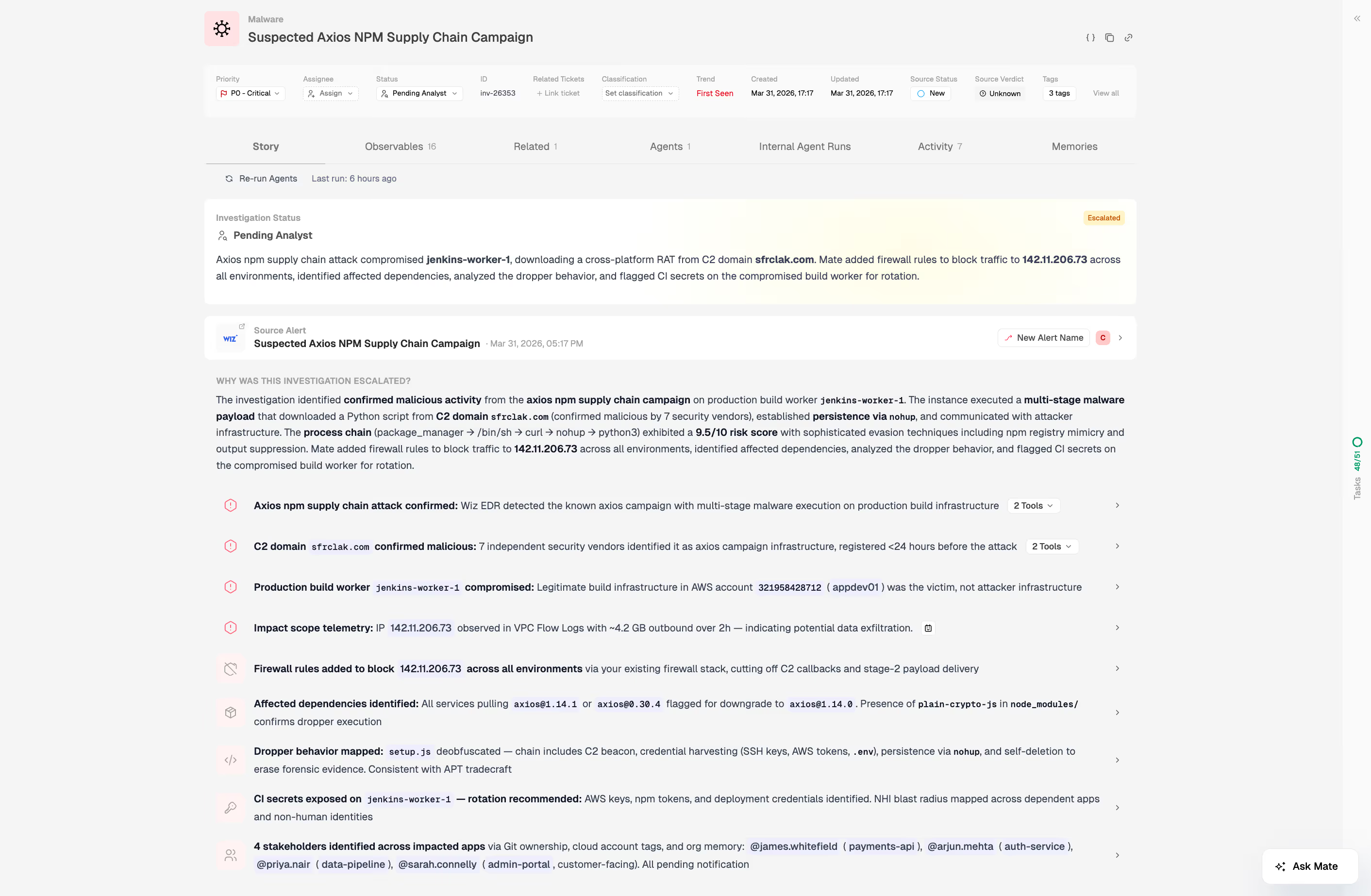
A healthcare institution's cloud environment triggered a Wiz alert from a compromised Axios package. In supply chain attacks every second counts. Evidence was already self-deleting. A Python RAT had begun beaconing to attacker infrastructure. And the CI/CD pipeline, with its source code, build secrets, and downstream deployment systems, was in the crosshairs.
Mate’s AI SOC agents investigated and successfully remediated the attack. This post describes the approach that Mate took, to successfully conclude the incident.
The Attack: A Compromised Axios Package
A threat actor compromised the npm distribution of Axios, a widely used JavaScript HTTP client, and published malicious versions that functioned as a dropper, executing a staged payload sequence upon installation. The malicious package downloaded a second-stage Python-based remote access trojan from attacker-controlled infrastructure at sfrclak.com:8000, established persistence, then self-deleted to remove forensic evidence. The target was the organization's CI/CD pipeline, a high-value environment where a successful foothold means access to source code, build secrets, and downstream deployment systems.
Step 1: Triage and Prioritization
The first question in any supply chain incident is how serious it is and how far it has spread.
Mate triaged hundreds of active alerts in the environment and elevated this incident to P0 priority. The alert arrived to the analyst pre-investigated: the full attack chain had already been reconstructed, affected resources had been profiled, and all relevant context had been assembled across the security stack. There was no manual enrichment queue, no waiting for threat intelligence lookups to return, and no need to pivot between tools to piece together what happened.
Step 2: Full Process Chain Analysis
To understand what an attacker did, you need to see everything they touched, in sequence, without gaps.
Mate reconstructed the complete execution path from the initial package manager installation through to second-stage payload execution. Every command executed by the malicious dependency was analyzed and attributed: the dropper script, the download from the C2 server, the Python RAT deployment, and the self-deletion routine. This provided an unambiguous picture of attacker intent and confirmed the full scope of what executed on the affected system.
Step 3: Threat Intelligence and Domain & IP Prevalence
Knowing what the attacker used is only half the picture. The critical question is whether that infrastructure had appeared in the environment before.
Mate ran automated threat intelligence against all identified malicious C2 domains and IP addresses. In parallel, it performed domain and IP prevalence analysis across the organization's full security infrastructure: DNS logs, cloud runtime telemetry, device timelines, and network logs.
The result was definitive. Zero prior presence of the malicious infrastructure anywhere in the environment. This ruled out pre-existing lateral movement and confirmed that the attack was detected at an early stage, before the attacker had established any meaningful foothold beyond the initial execution attempt.
Step 4: Cloud Resource and Secrets Exposure Analysis
In a CI/CD attack, the blast radius extends far beyond the infected host. The real risk is what the attacker could reach from there.
Because the attack targeted a CI/CD pipeline, Mate performed a risk analysis on all cloud resources connected to the affected environment to identify which secrets could have been exposed or compromised during the incident window. This step determines the true blast radius: which repositories are affected, which downstream services may have been touched, and what credential rotation is required. Mate surfaced this analysis automatically as part of the initial investigation, without requiring manual dependency tracing by the analyst.
Why Speed Is the Deciding Factor
Supply chain attacks exploit trusted processes. A legitimate package manager running a legitimate install command is not inherently suspicious. The malicious behavior only becomes detectable once execution begins, and by that point, in a manually-driven SOC, the investigation has not yet started. In supply chain attacks specifically, evidence is deleted faster than most teams can respond, and may be gone before investigation begins.
The gap between initial execution and active analyst investigation is where attackers operate. In this incident, that gap was compressed to near-zero. Mate's agents began investigation at the moment of alert generation, which meant the response team had full situational awareness before making any containment decisions, rather than building that awareness under time pressure after the fact.
This matters particularly for healthcare institutions, where CI/CD environments frequently hold production secrets, service account credentials, and access to regulated data systems, including systems that touch patient data and clinical infrastructure. Knowing the precise scope of secret exposure within minutes of detection, rather than hours, directly affects the speed and accuracy of the remediation response.
Recommended Response Actions
Based on the investigation findings, Mate's agents produced a structured response plan:
1. Root cause identification. Examine source code and locate the dependency files containing the compromised Axios version. Confirm exactly where and how the malicious package entered the build.
2. CI/CD pipeline tracing. Identify the specific repository that triggered the build which executed the malicious dependency. Tracing the build lineage confirms whether any other pipelines were exposed to the same package.
3. Secrets exposure assessment. Determine which secrets were attached to the CI server during the potential compromise window. This assessment drives rotation priorities, knowing which credentials to rotate, in what order, and on what timeline.
4. Network containment. Block the identified malicious DNS domains and IP addresses at both layer 4 and layer 7 firewalls. Severing C2 communication paths is the immediate priority while root cause analysis and rotation proceed in parallel.
Conclusion
Investigating a supply chain attack is a race against an attacker who has already started the clock. The dropper self-deletes. The RAT beacons silently. Evidence degrades. Every minute without full situational awareness is a minute the attacker can use.
The healthcare institution contained the threat quickly not because the attack was unsophisticated, but because the investigation was complete before containment decisions needed to be made. Full process chain visibility, confirmed domain and IP prevalence, and secrets exposure analysis were all in hand within seconds of the initial alert.
The agents did not replace analyst judgment. They ensured that judgment was applied to validated findings rather than spent on manual data gathering.
As supply chain attacks continue to mature, the organizations best positioned to respond are those with SOC capabilities that operate at the speed of detection, not the speed of manual investigation.
FAQs
Supply chain attacks execute through trusted processes, progressing from dependency installation to payload execution and persistence.
- Trace execution from dependency download to second-stage malware.
- Identify persistence mechanisms and self-deletion behavior.
- Reconstruct full process chains across systems.
Speed is critical because attackers delete evidence and establish control before manual investigations typically begin.
- Measure time between execution and investigation.
- Prioritize immediate automated analysis at alert generation.
- Capture volatile artifacts before they disappear.
Key indicators include unexpected external downloads, execution of secondary payloads, and self-deleting scripts.
- Detect outbound connections to unknown domains.
- Identify execution of non-native scripts (e.g., Python from Node).
- Monitor for file deletion patterns post-execution.
Learn how to check if you’re impacted and if the npm package is compromised.
Attackers target CI/CD pipelines to access source code, secrets, and downstream deployment systems.
- Trace which pipelines executed the malicious package.
- Identify accessible secrets and environment variables.
- Map downstream systems affected by the pipeline.
Mate automatically reconstructs the full attack chain and enriches alerts with all relevant context at ingestion time.
- Aggregates data across WAF, EDR, cloud, and CI/CD systems.
- Builds a complete execution timeline instantly.
- Presents analysts with ready-to-act intelligence.
Discover Mate’s Security Context Graph.
Mate analyzes connected resources and exposed secrets to map the full impact of the compromise.
- Identifies all connected cloud resources and repositories.
- Enumerates secrets accessible during the attack window.
- Prioritizes credential rotation based on exposure risk.
Learn more about Mate, book a demo.
Confirm persistence by analyzing process execution, file system changes, and outbound communication attempts.
- Detect RAT deployment and background processes.
- Look for artifacts in temporary directories like /tmp.
- Correlate with outbound beaconing activity.





